Vendor Due Diligence: The HR Leader’s Guide to Clearing Security Hurdles
You’ve found the perfect recruitment automation platform. It solves your scheduling bottlenecks and provides the candidate insights you’ve been desperate for. You’re ready to sign, but then you hit the wall: Procurement and Legal.
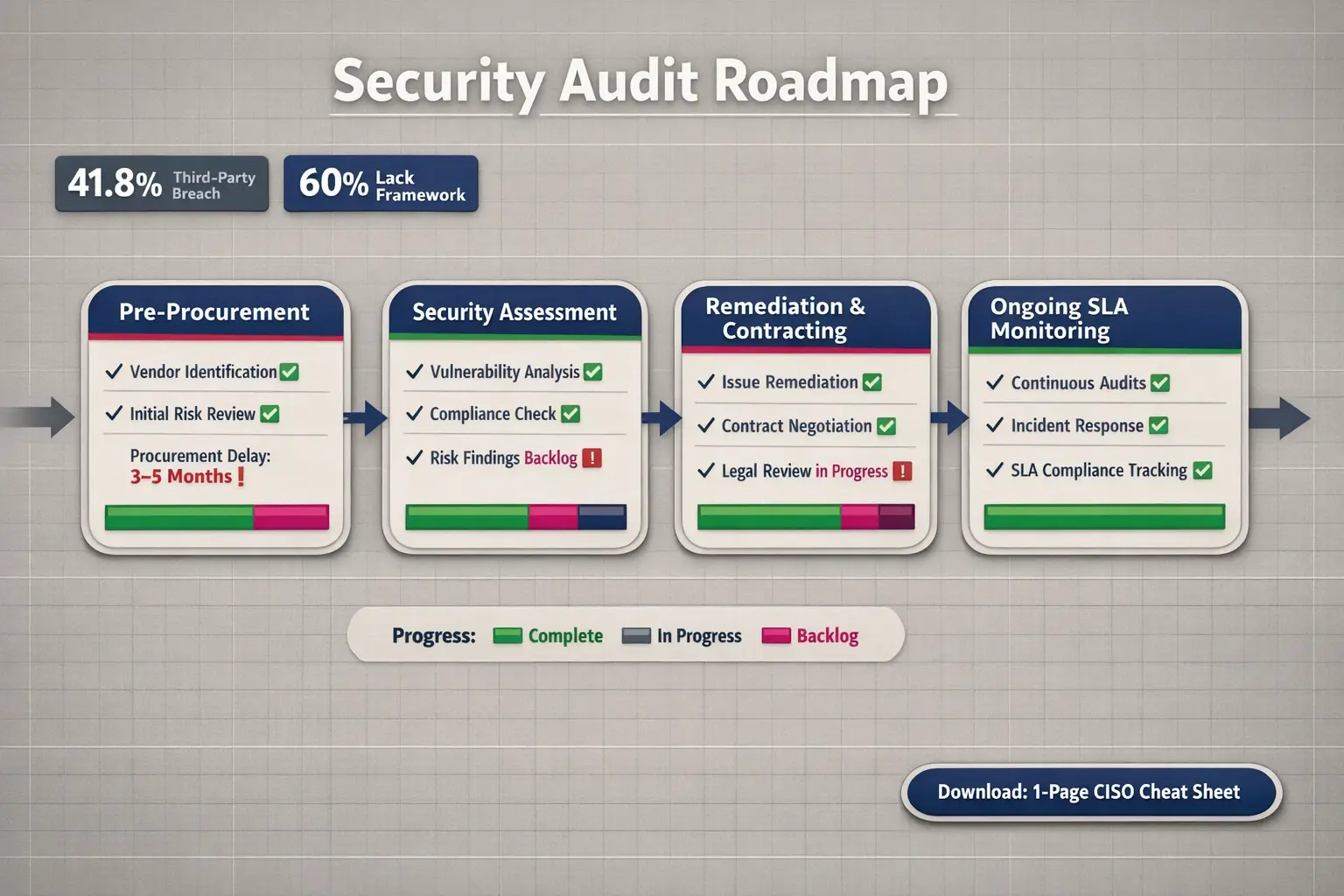
Suddenly, your implementation timeline pushes out by months. You aren’t alone. According to Gartner, the lack of standardized frameworks for HR vendor risk management causes average procurement delays of 3–5 months.
In 2025, buying HR tech isn’t just about features; it’s about passing the “CISO test.” With 41.8% of data breaches in high-tech sectors originating from third-party vendors, your security team isn’t trying to be difficult—they are trying to survive.
Here is how you navigate vendor due diligence, audit your potential partners, and get your tech stack approved faster.
The New Standard for HR Tech Evaluation
The days of simply checking for a privacy policy are over. To evaluate modern AI recruitment tools like Upfound AI, you need a “compliance-first” mindset. This means looking beyond the vendor’s direct security to understand their entire data ecosystem.
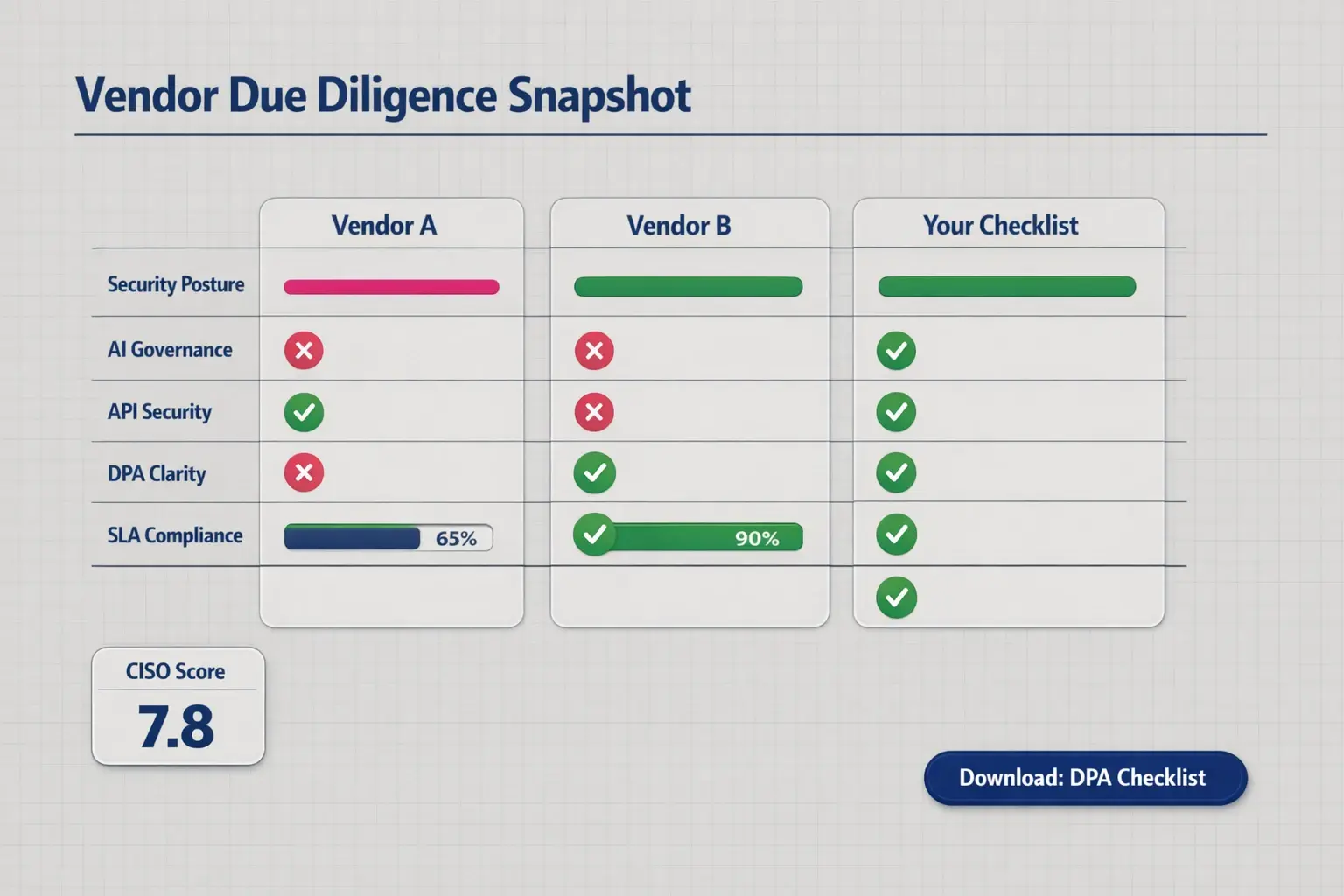
Your Due Diligence Checklist
When evaluating providers, your security audit must cover three non-negotiable pillars:
- Fundamental Security: Look for SOC2 Type II certification and encryption (both at rest and in transit). If a vendor cannot provide a recent SOC2 report, the conversation should end there.
- AI Governance & Bias: This is where most competitors fail. With regulations like NYC Local Law 144 and the EU AI Act, you must verify “Algorithmic Transparency.” Ask for their latest bias audit results.
- API & Integration Safety: How does the tool talk to your ATS? Ensure they use secure, limited-access APIs rather than asking for broad, unchecked database permissions.
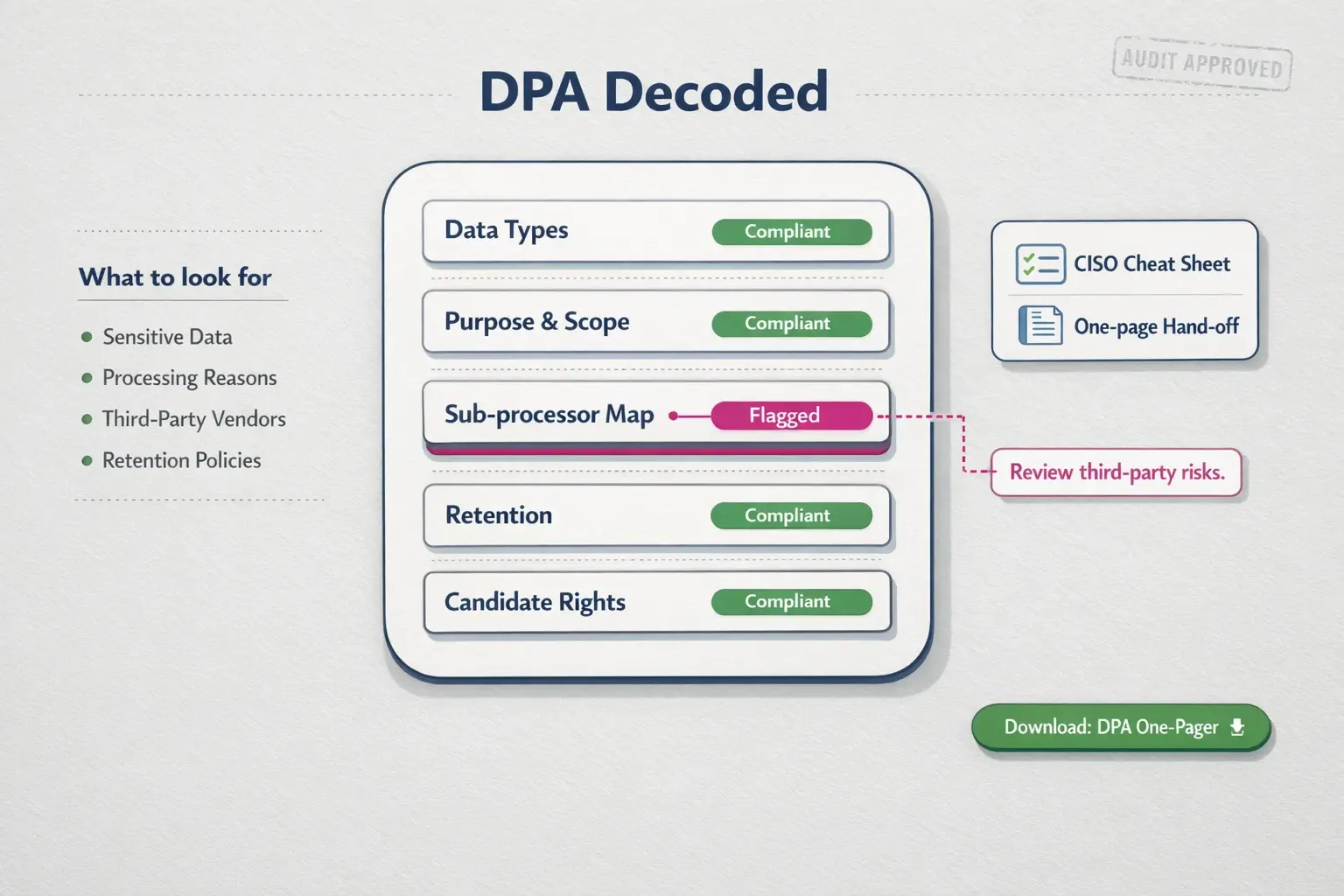
Decoding the Data Processing Agreement (DPA)
The DPA is often the document that stalls deals. It outlines how a vendor handles your data. You don’t need to be a lawyer to spot the red flags, but you do need to understand the distinction between Candidate Data Rights and Employee Data Rights.
A robust DPA clarifies who owns the data (you do) and how it is deleted upon request. If a vendor is vague about their data retention policies or sub-processor liabilities, your Legal team will reject them.
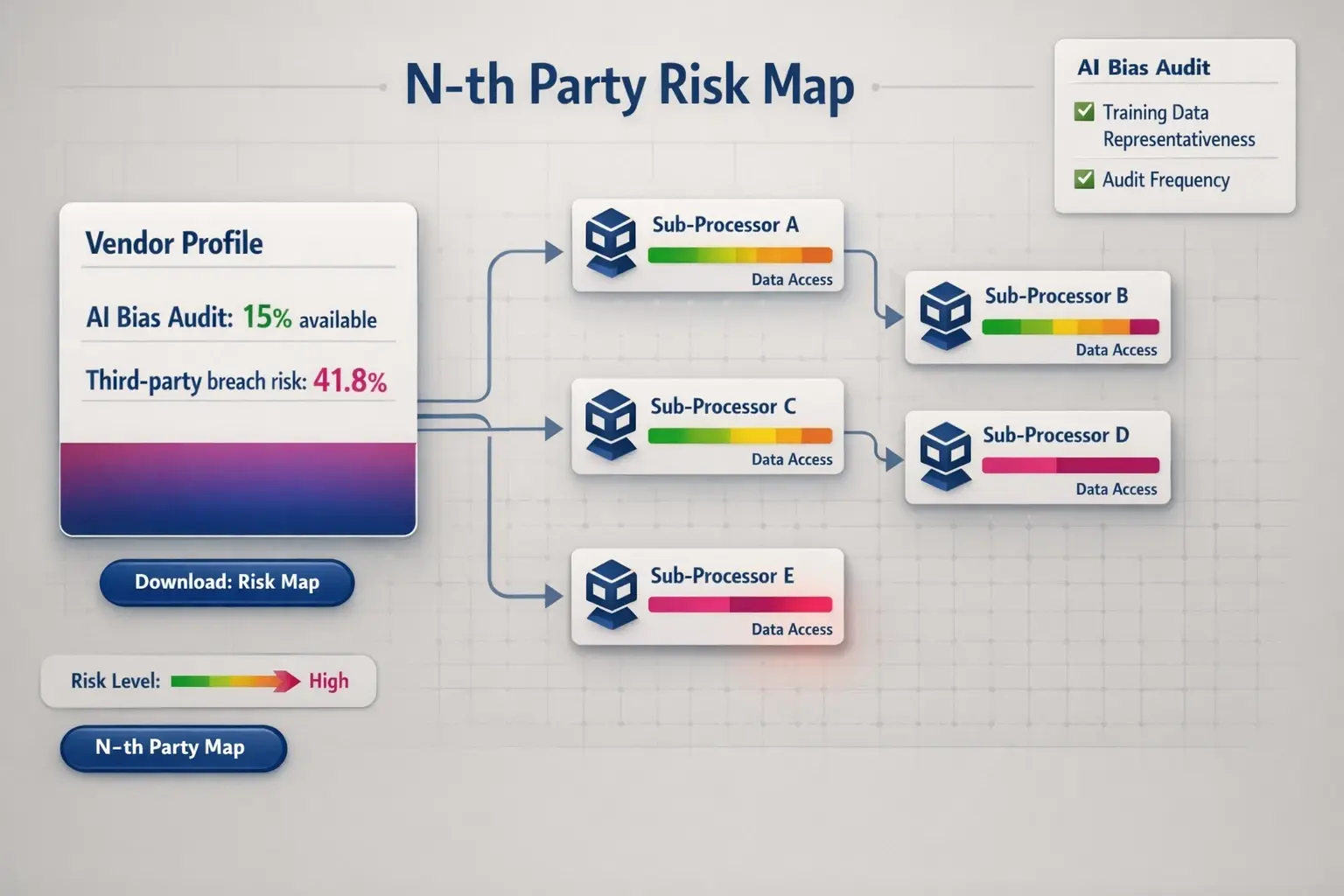
The Hidden Risk: N-th Party Exposure
Your vendor is secure, but what about their vendors? This is called N-th party risk.
If your recruitment platform uses a third-party transcription service that lacks security compliance, your data is exposed. You need to map out the vendor’s sub-processors. At Upfound AI, we maintain strict oversight of our entire data chain to ensure there are no weak links in your security posture.
The CISO Handoff: Speeding Up Approval
To cut that 3-5 month delay down to weeks, prepare a “CISO Handoff” package. Do not send your IT team a marketing brochure; send them the technical specs they care about:
- The SOC2 Report
- The API Documentation
- The AI Bias Audit Certificate
- The SLA Compliance limits
Frequently Asked Questions
What specific AI regulations should I check for?
Focus on NYC Local Law 144 (bias audits for automated employment decision tools) and the EU AI Act. Even if you aren’t in these regions, these are the global gold standards for safety.
How do I verify if an ATS integration is secure?
Request documentation on their API protocols. A secure integration uses OAuth tokens and encrypted endpoints, ensuring the vendor only accesses the specific data fields required for the job.
Why is an SLA important for risk management?
Service Level Agreements (SLAs) aren’t just about uptime; they dictate how quickly a vendor must notify you in the event of a security breach. Strict notification windows are critical for your own compliance.
The Upfound AI Advantage
We built Upfound AI to be more than just an automation tool; we built it to be a secure infrastructure for global hiring teams. By prioritizing data privacy, rigorous bias auditing, and transparent sub-processor management, we help you satisfy your CISO’s requirements so you can get back to what matters: hiring the best talent, faster.
Ready to secure your hiring pipeline? Explore our security documentation today.